The software supply chain has just witnessed one of its most significant breaches of 2026. Axios, the ubiquitous JavaScript HTTP client boasting over 100 million weekly downloads, was compromised in a sophisticated campaign that turned a trusted development tool into a delivery vehicle for a cross-platform Remote Access Trojan (RAT).
In this deep dive, we break down how the attack bypassed modern security headers, the technical mechanics of the "Phantom Dependency" strategy, and the urgent steps your DevOps team must take to secure your pipeline.
The Incident: Timeline of a 100M-Download Compromise
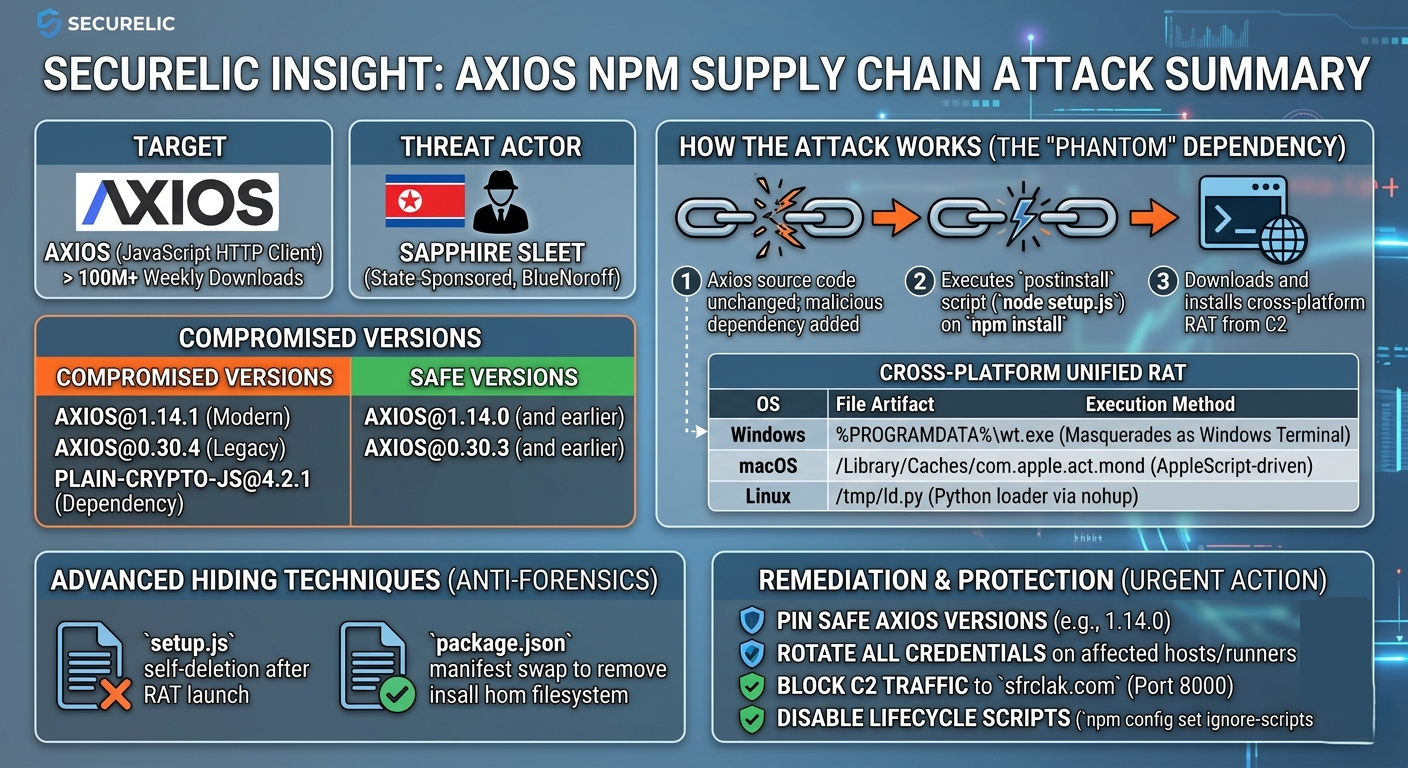
On March 31, 2026, threat actors successfully hijacked the npm account of a lead Axios maintainer. By bypassing the project’s standard GitHub-to-NPM CI/CD pipeline, the attackers published two "poisoned" versions directly to the official registry:
- Axios 1.14.1 (Modern release)
- Axios 0.30.4 (Legacy release)
The "Phantom Dependency" Strategy
The attackers did not modify the core Axios source code a move designed to evade static analysis tools that monitor repository changes. Instead, they performed a surgical manifest-only injection, adding a new dependency: ([email protected].)
This package was a "wolf in sheep’s clothing." The threat actor (identified as Sapphire Sleet, a North Korean-nexus group) had published a clean version (4.2.0) eighteen hours earlier to build a "safe" reputation before releasing the malicious patch.
Technical Breakdown: How the RAT Operates
When a developer or a CI/CD runner executes npm install, the postinstall hook in plain-crypto-js triggers node setup.js. This script functions as a Stage-1 dropper with highly advanced capabilities.
1. XOR Obfuscation and OS Fingerprinting
The setup.js loader uses a layered XOR cipher (Key: OrDeR_7077) to reconstruct malicious strings at runtime. It identifies the host's operating system and reaches out to a Command & Control (C2) server at sfrclak[.]com:8000.
2. The Multi-Platform Payload
The C2 delivers a secondary "Unified RAT" tailored to the victim's architecture:
| Operating System | Payload Artifact | Execution Method |
| Windows | %PROGRAMDATA%\wt.exe | Masquerades as "Windows Terminal"; establishes registry persistence. |
| macOS | /Library/Caches/com.apple.act.mond | AppleScript-driven download; identified as the WAVESHAPER backdoor. |
| Linux | /tmp/ld.py | Python-based loader executed via nohup for background persistence. |
3. Anti-Forensic "Self-Erasure"
To keep the infection silent, the malware performs an immediate cleanup. After the RAT is active, setup.js deletes itself and overwrites the package.json manifest with a clean decoy. If a security engineer checks the node_modules folder minutes later, the malicious hooks have vanished.
Why OIDC Provenance Didn't Save Us
The most alarming aspect of this breach is that legitimate Axios releases use OIDC (OpenID Connect) Trusted Publishing. This cryptographically links npm packages to specific GitHub Actions.
However, because the npm registry still allows "Mixed Mode" publishing, the attacker was able to use a stolen manual API token to push the poisoned versions. The registry accepted the upload despite it lacking the SLSA build attestations that have guarded Axios for over a year.
Securelic Remediation Guide: How to Respond
If your organization uses Axios, follow this emergency checklist immediately:
1. Audit and Pin Versions
Check your package-lock.json or yarn.lock for the malicious versions. Immediately downgrade and pin to the last known safe releases:
- Safe Modern:
[email protected] - Safe Legacy:
[email protected]
Securelic Tip: Avoid using carets (
^) or tildes (~) in yourpackage.jsonfor critical dependencies. Use exact versioning to prevent auto-upgrades to unvetted patches.
2. Flush Caches and Rotate Secrets
Run npm cache clean--force to ensure your build servers aren't pulling the poisoned versions from a local cache.
Assume Compromise: If the malware was installed, assume all environment variables (AWS keys, SSH tokens, NPM secrets) on that machine have been exfiltrated. Rotate them now.
3. Implement Egress Filtering
The Axios RAT requires a connection to sfrclak[.]com. Configure your CI/CD firewalls to block all outbound traffic except to a strictly defined allowlist of package registries.
4. Global Script Hardening
Disable postinstall scripts globally unless explicitly required:
Conclusion: The New Normal of Dependency Management
The Axios attack is a stark reminder that even the most trusted libraries are subject to account takeovers. At Securelic, we advocate for a "Zero Trust" approach to dependencies. Monitoring for version drift and enforcing build provenance are no longer optional—they are the baseline for survival in the 2026 threat landscape.
Stay Secure
C2 Domain: sfrclak[.]com
C2 IP: 142.11.206.73
File Hashes (RAT):
macOS: 92ff08773995ebc8d55ec4b8e1a225d0d1e51efa4ef88b8849d0071230c9645a
Linux: fcb81618bb15edfdedfb638b4c08a2af9cac9ecfa551af135a8402bf980375cf