Security Scanners Overview
Explore our suite of security scanners designed to help you discover, analyze and continuously protect your attack surface.
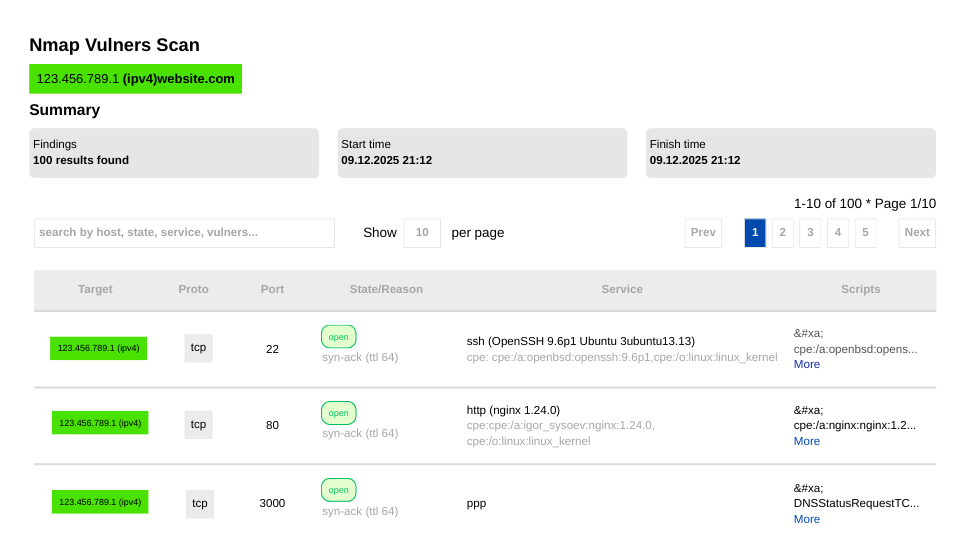
Map Your Network Infrastructure
Nmap scans your IP ranges to discover live hosts, open ports and running services. It goes beyond simple detection by identifying operating system versions and service protocols, giving you a clear picture of what is accessible from the outside.
By detecting open ports and service versions, it highlights potential entry points that attackers could exploit. It helps you verify firewall configurations and ensure only necessary services are exposed to the public.
The result is a comprehensive network map that serves as the foundation for your security strategy, ensuring you know exactly what assets need protection.
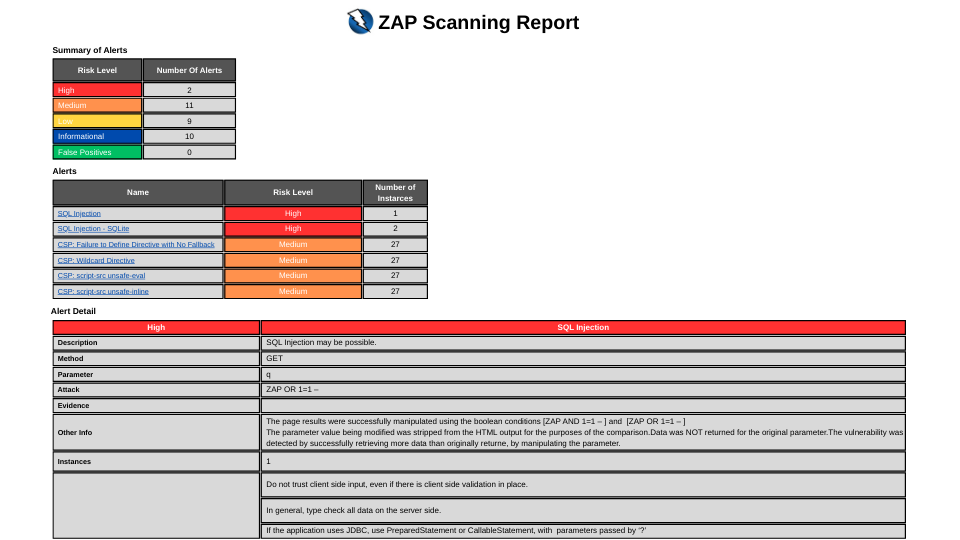
Automated Web App Security Testing
ZAP acts as a man in the middle proxy to intercept and analyze traffic between your browser and web application. It performs active attacks to identify critical risks such as SQL Injection, Cross Site Scripting (XSS) and broken access controls.
Designed for modern web apps, it helps you find vulnerabilities that static analysis might miss. It effectively tests your application's resilience against real world attack vectors without needing access to the source code.
Regular scans with ZAP ensure your application meets security standards like the OWASP Top 10, allowing you to fix critical flaws before deployment.
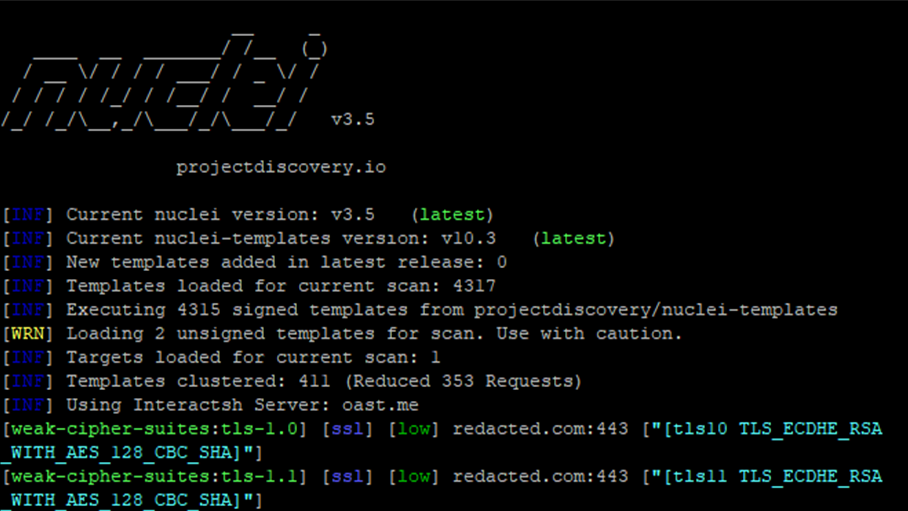
Detect Modern Vulnerabilities Rapidly
Nuclei sends requests across targets based on templates, leading to zero false positives and fast scanning on large numbers of hosts. It checks for specific CVEs, misconfigurations and exposed panels using a constantly updated database.
Its template based architecture allows it to detect the latest threats moments after they are disclosed. Whether it's a critical zero-day or a simple configuration error, Nuclei identifies it with high precision.
This tool integrates seamlessly into your workflow, providing actionable results that help you patch high severity vulnerabilities across your entire infrastructure immediately.
Uncover Hidden Assets and Shadow IT
Subfinder aggregates data from leading passive DNS sources, search engines and internet archives to list valid subdomains for your target. It does this without sending direct traffic to the target, ensuring a stealthy discovery process.
This discovery phase is crucial for finding 'Shadow IT' forgotten development servers or legacy subdomains that are often left unsecured. It expands your known attack surface beyond just the main domain.
By providing a complete list of subdomains, it ensures that your subsequent vulnerability scans cover 100% of your organization's external footprint.

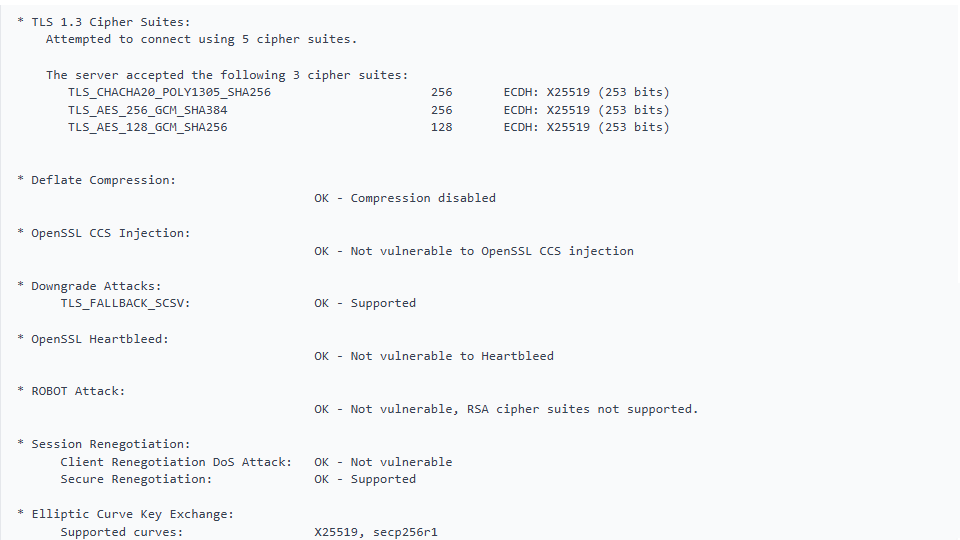
Validate SSL/TLS Configuration
SSLyze connects to your servers to analyze their SSL/TLS setup. It checks for certificate validity, supported cipher suites and the presence of outdated protocols like SSLv3 or TLS 1.0 that could compromise data integrity.
It specifically looks for well known vulnerabilities such as Heartbleed, ROBOT or OpenSSL padding oracles. It ensures your encryption standards meet modern compliance requirements.
The scan provides a clear report on your encryption posture, helping you prevent man in the middle attacks and ensuring secure communication for your users.
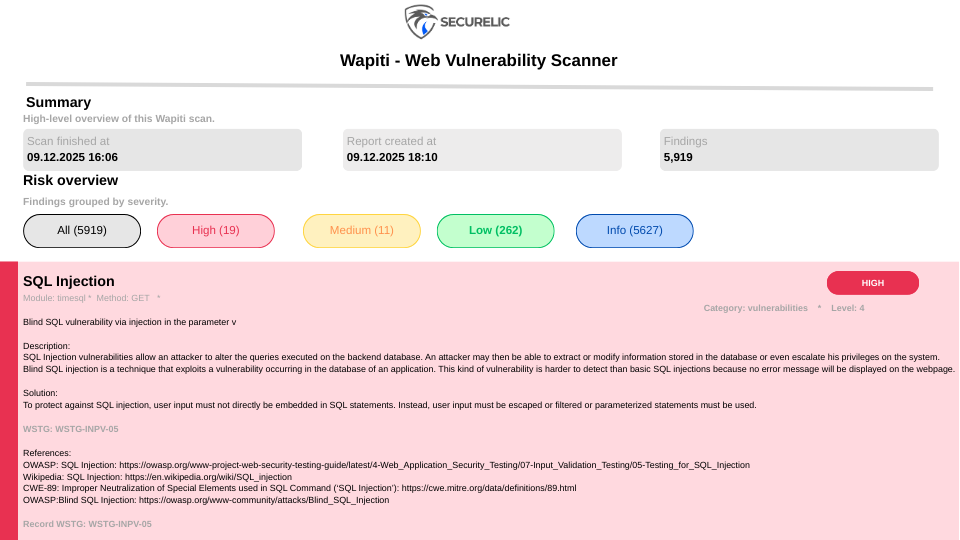
Audit Your Web Forms and Inputs
Wapiti works by crawling the webpages of the deployed web application and injecting 'fuzzing' payloads. It tests forms, URL parameters and headers to see if the script is vulnerable to injection attacks.
It effectively detects File Disclosure, Database Injection, XSS and Command Execution vulnerabilities. Unlike source code scanners, it tests the application in its running state, simulating an external hacker.
This allows you to identify and fix logic errors and input validation problems that only appear when the application is live and interacting with a server.
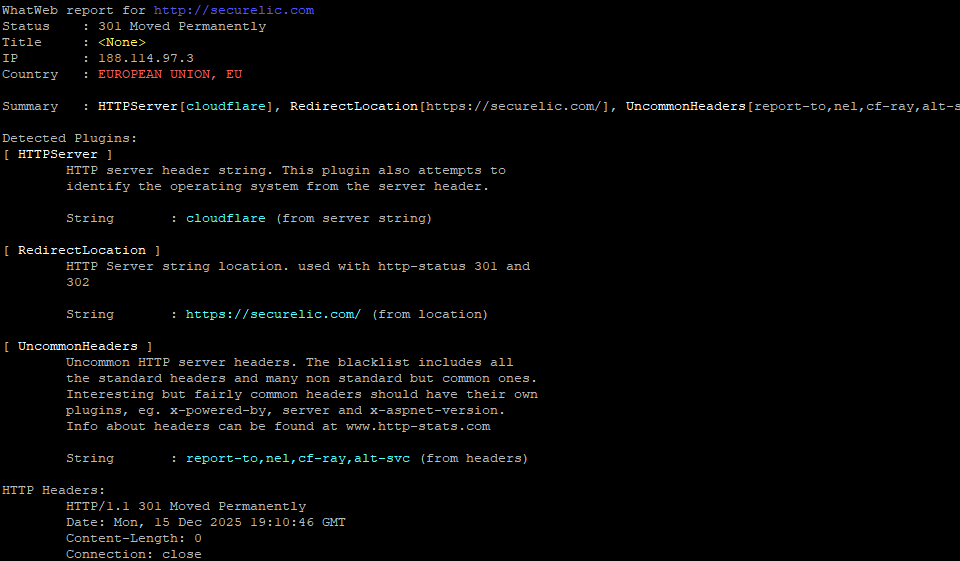
Identify Your Technology Stack
WhatWeb acts as a fingerprint scanner for your web presence. It recognizes Content Management Systems (CMS), blogging platforms, statistic/analytics packages, JavaScript libraries, web servers and embedded devices.
Knowing the exact version of the software running on your server is critical for vulnerability management. It allows you to cross reference your stack against known CVE databases to find version specific exploits.
It provides a detailed inventory of your web technologies, helping you manage updates and retire outdated or unsupported software components.
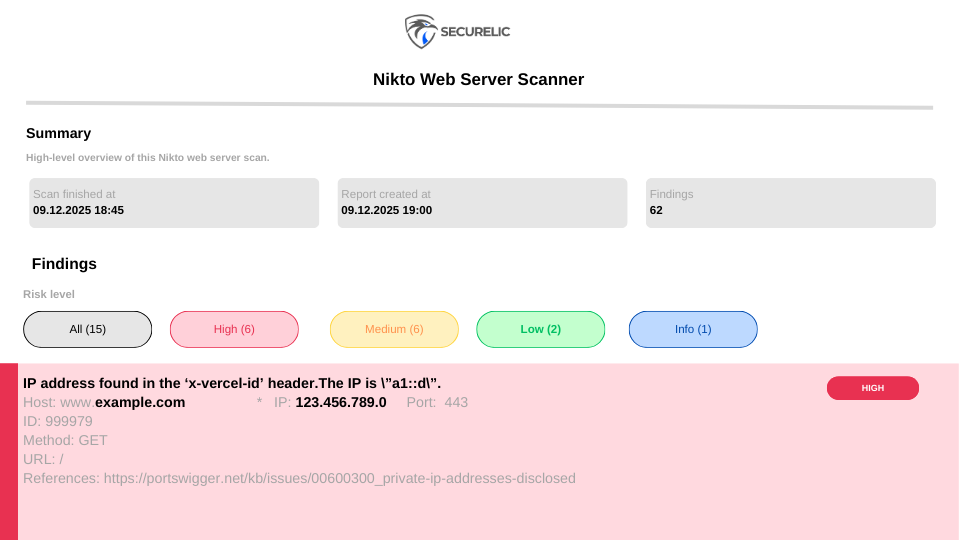
Comprehensive Web Server Scanning
Nikto scans your web server for over 6,700 potentially dangerous files and programs. It checks for outdated server versions and specific version related problems that could be exploited.
It is particularly effective at finding default installation files, insecure server configurations and 'low hanging fruit' that are often overlooked during manual testing.
Using Nikto helps you harden the web server itself, ensuring the platform hosting your application is as secure as the application code.
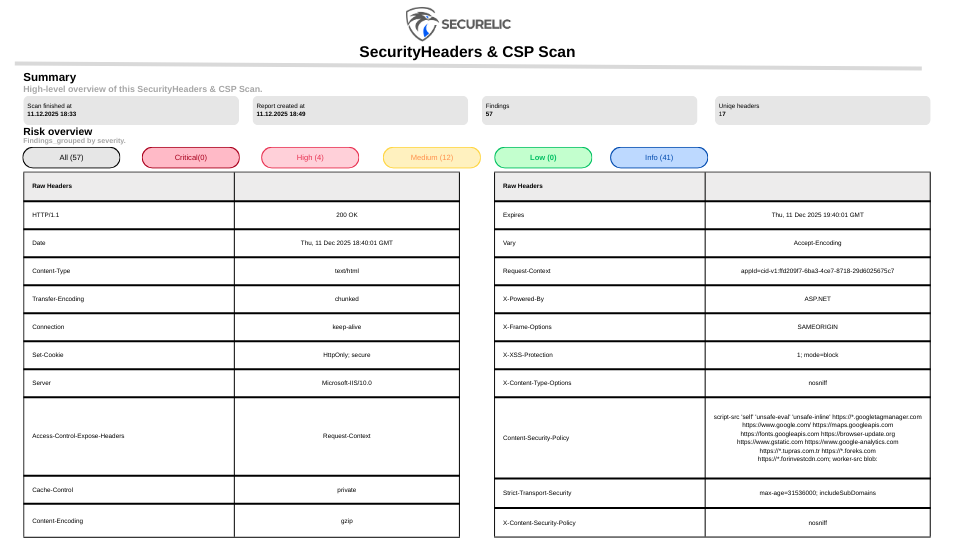
Strengthen Browser Side Security
This scanner inspects the HTTP headers your server sends to visitors. It checks for the presence and correct configuration of headers like Content Security Policy (CSP), HSTS and X Frame Options.
Properly configured headers are the first line of defense against client side attacks such as Cross Site Scripting (XSS), Clickjacking and protocol downgrade attacks.
By optimizing these headers, you instruct modern browsers on how to behave securely when loading your site, significantly reducing the impact of potential attacks on your users.
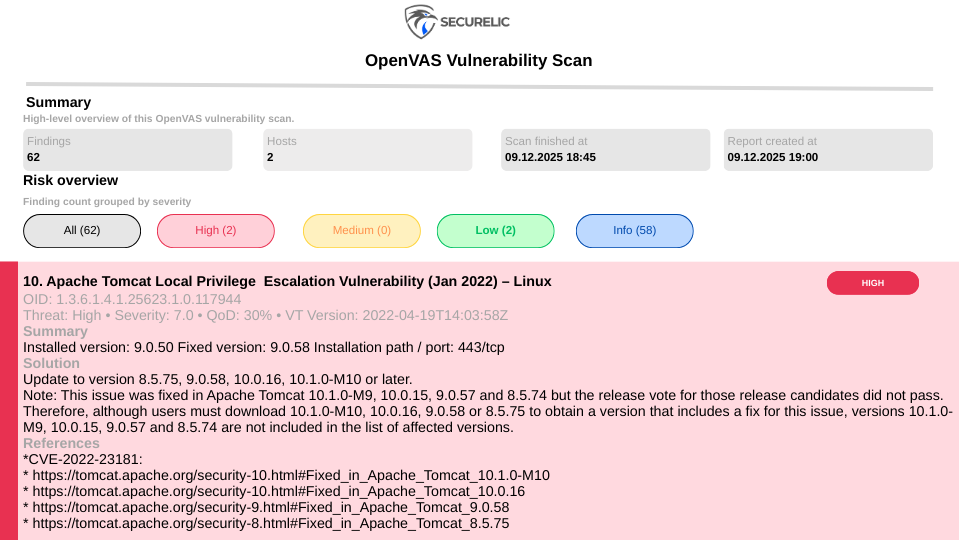
Holistic Vulnerability Assessment for Your Entire Infrastructure
OpenVAS delivers a structured and reliable assessment of your infrastructure’s security posture. It evaluates operating systems, network services, applications and installed components using a comprehensive and continuously updated set of vulnerability tests.
By correlating detected versions, configurations and exposed services with known security issues, it identifies risks that may be leveraged in real world attacks including those not immediately visible during routine checks.
This approach provides a clear view of your environment’s overall security state, enabling you to prioritize remediation efforts and strengthen the entire infrastructure with confidence.