MongoBleed (CVE-2025-14847): Risk, Detection and How to Protect Your Data
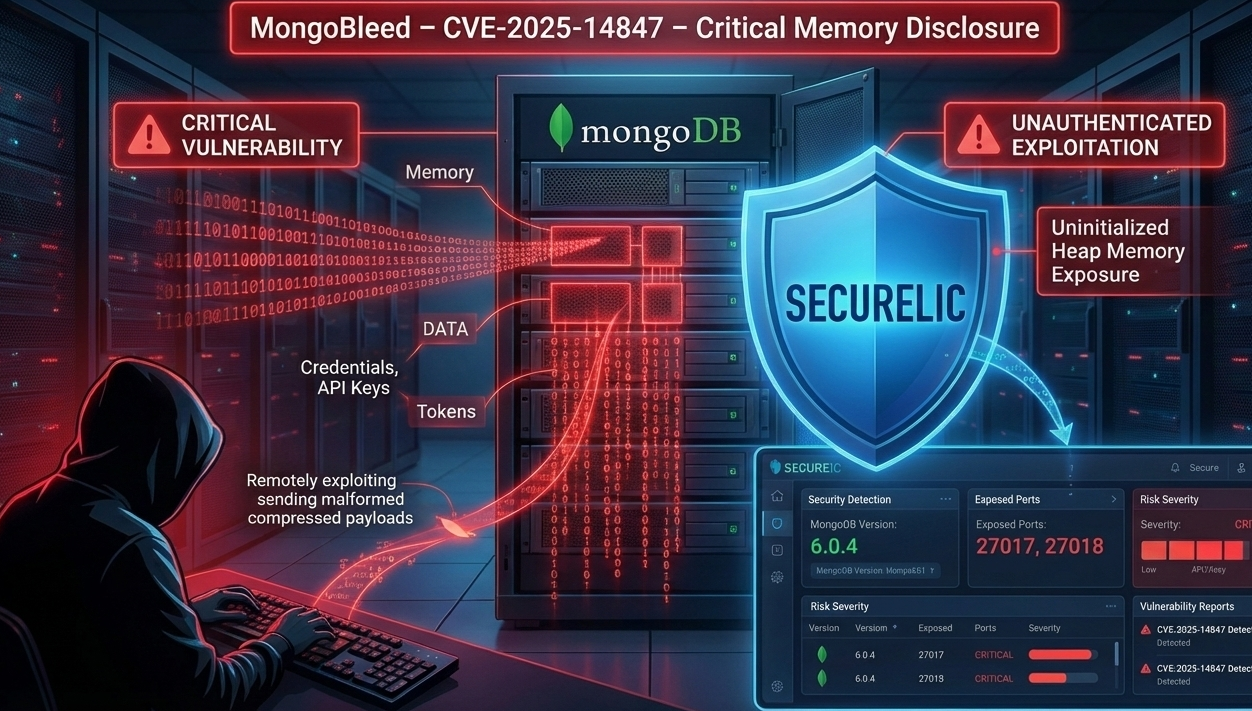
In late 2025, a critical vulnerability known as MongoBleed was disclosed in the widely used NoSQL database MongoDB. This flaw, tracked as CVE-2025-14847, has the potential to expose sensitive data from database memory to unauthenticated attackers making it a serious risk for organizations relying on MongoDB for backend data storage.
What Is MongoBleed (CVE-2025-14847)?
MongoBleed is a memory disclosure vulnerability caused by improper handling of compressed network messages in MongoDB’s internal protocol using the zlib compression library. Specifically, mismatched length fields in zlib compressed headers may cause MongoDB servers to respond with uninitialized heap memory, which can contain sensitive data such as credentials, tokens, configuration secrets, API keys, or other internal information.
What makes this vulnerability particularly dangerous is that it is remotely exploitable without any authentication attackers do not need valid credentials or user interaction to trigger the flaw.
Who Is Affected?
MongoBleed affects a very broad range of MongoDB Server versions, including:
MongoDB Server 8.2.0 through 8.2.2
MongoDB Server 8.0.0 through 8.0.16
MongoDB Server 7.0.0 through 7.0.27
MongoDB Server 6.0.0 through 6.0.26
MongoDB Server 5.0.0 through 5.0.31
MongoDB Server 4.4.0 through 4.4.29
All MongoDB Server 4.2 and 4.0 releases
All MongoDB Server 3.6 releases
Patched versions containing fixes are now available (e.g., 8.2.3, 8.0.17, 7.0.28, 6.0.27, 5.0.32, 4.4.30).
Why This Vulnerabilities Matter
Unauthenticated Exploitation
Since MongoBleed requires no authentication, any exposed MongoDB instance reachable over the network could be at risk attackers could simply send crafted network requests to extract internal memory data.
Sensitive Data Exposure
Internal memory may contain high value targets, such as passwords, session tokens, infrastructure keys and configuration details. Even partial leaks can be combined to escalate attacks or pivot into deeper systems.
Widespread Impact
Because MongoDB is widely deployed across industries, from startups to large enterprises, the attack surface for this vulnerability is significant. Analysts estimate tens of thousands of instances remain exposed online.
Threat Actor Motivation
Attackers targeting MongoBleed are typically motivated by:
Credential harvesting - extraction of administrative or user credentials
Cloud key theft - gaining access to cloud infrastructure
Session token leakage - enabling session hijacking
Data exfiltration - stealing sensitive business or customer data
The fact that exploitation is simple to attempt and requires no privileged access greatly increases the threat level for attackers of varying skill levels.
Immediate Actions
Patch MongoDB Instances
The primary mitigation is upgrading to a patched release of MongoDB as soon as possible.
Restrict Network Access
Detection Opportunities With Securelic
At Securelic, proactive vulnerability scanning is a core defense strategy. Our open source powered vulnerability scanner can help you:
Identify MongoDB instances exposed online
Detect versions vulnerable to CVE-2025-14847
Simulate and detect malformed network payload responses
Generate actionable risk reports prioritizing MongoBleed exposure
Integrate into your CI/CD and DevOps workflows to catch future risks early
By regularly scanning your infrastructure for known CVEs, including memory disclosure issues like MongoBleed, Securelic provides continuous insight into your security posture.
Best Practices for Remediation
To reduce risk and prevent exploitation:
Keep all database systems updated with the latest security patches
Avoid exposing database ports publicly whenever possible
Implement network segmentation to limit lateral movement
Monitor network traffic for anomalous compression or malformed packetsUse runtime protection tools to flag suspicious database responses
Combined with vulnerability scans and automated alerts, these practices significantly reduce the chance of successful exploitation.
Summary
MongoBleed (CVE-2025-14847) is a critical, easily exploitable vulnerability in MongoDB servers that can leak sensitive server memory to unauthenticated attackers. Its widespread impact and simplicity of exploitation make it a top priority for remediation.
By applying patches immediately, restricting access and leveraging proactive scanning solutions like Securelic’s open source powered scanner, organizations can detect vulnerable deployments and protect their data before attackers strike.
Stay secure, stay vigilant and never underestimate the value of continuous vulnerability scanning.
This article is based on publicly available security advisories, threat intelligence reports and vendor disclosures to ensure accuracy and relevance.
References
Akamai Security Research
CVE-2025-14847: All You Need to Know About MongoBleed
https://www.akamai.com/blog/security-research/cve-2025-14847-all-you-need-to-know-about-mongobleed
eSecurity Planet
87,000+ MongoDB Instances Exposed by MongoBleed Vulnerability
https://www.esecurityplanet.com/threats/87k-mongodb-instances-exposed-by-mongobleed-vulnerability/
MongoDB Security Advisory
MongoDB Server Security Bulletin – CVE-2025-14847
https://www.mongodb.com/alerts
NIST National Vulnerability Database (NVD)
CVE-2025-14847 – MongoDB Memory Disclosure Vulnerability
https://nvd.nist.gov/vuln/detail/CVE-2025-14847
OX Security Research
MongoBleed: zlib Compression Memory Leak in MongoDB
https://www.ox.security/blog/attackers-could-exploit-zlib-to-exfiltrate-data-cve-2025-14847/
Upwind Security
CVE-2025-14847 MongoDB zlib Memory Disclosure Explained
https://www.upwind.io/feed/cve-2025-14847-mongodb-zlib-memory-disclosure
Securelic – Open Source Powered Vulnerability Scanning
Proactive Detection of Critical Infrastructure Vulnerabilities
https://securelic.com/