Securing data in transit is no longer just a compliance checklist; it is the foundation of digital trust. As cyber threats evolve and cryptographic standards deprecate, ensuring your servers use strong encryption settings is critical. Enter SSLyze a fast and powerful SSL/TLS scanning tool and Python library designed to analyze server configurations and uncover critical vulnerabilities.
Whether you are a system administrator hardening a web server, or a security researcher mapping an external attack surface, understanding how to leverage SSLyze is essential. In this guide, we will explore what makes this tool a staple in the cybersecurity community, how it integrates into penetration testing workflows, and how to scale your assessments with an SSLyze online scan.
Table of Contents
- What is SSLyze?
- Key Features of SSLyze
- sslyze | Kali Linux Tools: A Pentester's Companion
- Detecting Known TLS Attacks
- How to Run an SSLyze Online Scan
- Scaling SSL/TLS Automation with Securelic
What is SSLyze?
SSLyze - Fast and powerful SSL/TLS scanning tool is an open-source project written in Python that connects to a target server and analyzes its cryptographic posture. Unlike simple certificate checkers, SSLyze performs a deep dive into the server's configuration to ensure it uses strong cipher suites, robust elliptic curves, and valid certificates.
Because it is built as both a command-line tool and a Python library, it is highly favored by developers who want to integrate SSL/TLS testing directly into their automated security pipelines and CI/CD workflows.
Key Features of SSLyze
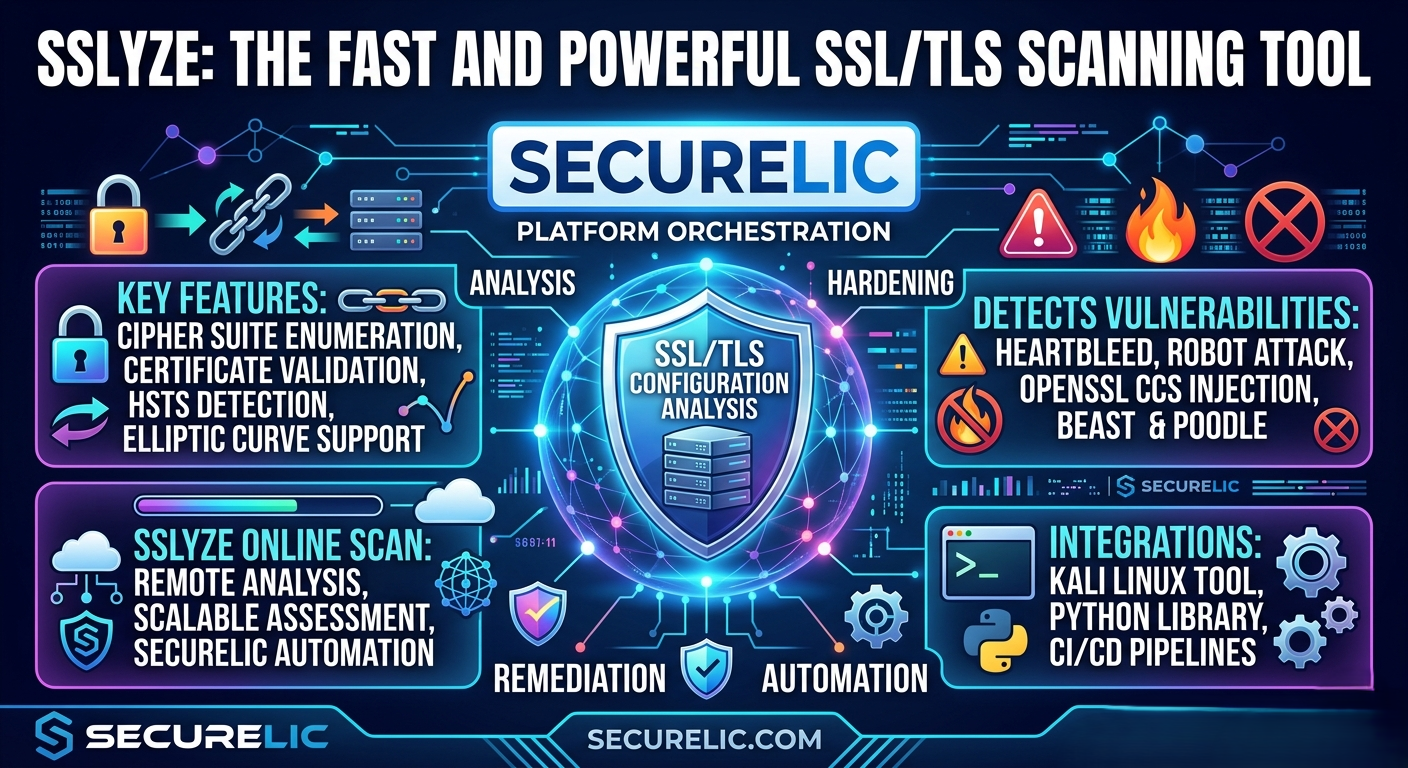
SSLyze stands out in the crowded field of vulnerability scanners due to its speed, accuracy, and comprehensive testing capabilities. Its primary features include:
- Cipher Suite Enumeration: Rapidly checks which cipher suites are supported by the server, flagging weak or deprecated encryption protocols (like SSLv2, SSLv3, or TLS 1.0).
- Certificate Validation: Verifies the trust chain of the server's certificate, checking for expiration dates, weak hashing algorithms (like SHA-1), and hostname mismatches.
- HTTP Strict Transport Security (HSTS): Analyzes the presence and configuration of HSTS headers to ensure browsers are forced to use secure connections.
- Elliptic Curve Support: Tests for modern elliptic curve configurations vital for Forward Secrecy.
sslyze | Kali Linux Tools: A Pentester's Companion
If you search for sslyze | Kali Linux Tools, you will quickly see why it is pre-packaged in the world's most popular penetration testing distribution. For ethical hackers and security engineers, SSLyze is the go-to utility during the reconnaissance and vulnerability assessment phases.
During an External Attack Surface Management (EASM) exercise, analysts use SSLyze alongside tools like Nmap and Subfinder to paint a complete picture of a target's perimeter. Its fast, multi-threaded engine allows pentesters to scan hundreds of endpoints rapidly, making it an indispensable asset in any Kali Linux toolkit.
Detecting Known TLS Attacks
A misconfigured TLS server can expose sensitive data to interception. SSLyze actively probes for susceptibility to historically devastating vulnerabilities, ensuring your infrastructure is fully patched against:
- Heartbleed: A critical flaw in OpenSSL that allows attackers to read the memory of the systems protected by the vulnerable versions.
- ROBOT (Return Of Bleichenbacher's Oracle Threat): An attack that allows RSA decryption and signing operations to be performed by an attacker.
- OpenSSL CCS Injection: A vulnerability that allows a man-in-the-middle attacker to intercept and decrypt traffic.
- POODLE & DROWN: Checks for fallback vulnerabilities related to outdated SSL versions.
How to Run an SSLyze Online Scan
While running SSLyze locally via the command line (pip install sslyze) is straightforward for a single host, enterprise environments require a more streamlined approach. Executing an SSLyze online scan allows teams to assess their infrastructure without managing local dependencies, Python environments, or firewall rules.
Online scanning removes the friction of manual tool execution. By inputting a target domain into a web-based interface, security teams can instantly generate comprehensive cryptographic reports, making it easier to share findings with stakeholders and developers.
Scaling SSL/TLS Automation with Securelic
Managing the execution of open-source tools like SSLyze, OWASP ZAP, and Nuclei across a growing, global infrastructure can become a logistical nightmare. While SSLyze is incredibly powerful, extracting its data and turning it into continuous, actionable intelligence requires a robust backend architecture.
This is where Securelic bridges the gap. As a cloud-based SaaS cybersecurity product, Securelic orchestrates the power of tools like SSLyze within a unified platform. Instead of running manual command-line scripts, Securelic allows you to:
- Automate Continuous Scanning: Schedule an SSLyze online scan across your entire external attack surface automatically.
- Centralize Intelligence: Consolidate findings from SSLyze with other automated reconnaissance data to prioritize API vulnerabilities and cryptographic flaws in one dashboard.
- Agentic AI Remediation: Leverage intelligent workflows to not only identify weak cipher suites but to provide developers with the exact configuration fixes needed for their specific web servers.
Don't let a deprecated cipher suite or an expiring certificate be the weak link in your security posture. Integrate the speed of SSLyze with the automated power of a modern cloud-based EASM platform.
[Ready to orchestrate your security? Explore Securelic today and take control of your attack surface.]