The cybersecurity landscape has reached a critical turning point. The newly released CrowdStrike 2026 Global Threat Report (analyzing data and trends from 2025) paints a stark picture of a world where traditional defenses are rapidly becoming obsolete.
In past years, we watched adversaries slowly adopt new tools, but 2025 was marked by the widespread, aggressive weaponization of Artificial Intelligence. Threat actors are now moving undetected across domains, bypassing heavily monitored endpoints and targeting unmanaged edge devices with unprecedented speed.
At Securelic, we dive deep into these industry leading intelligence reports so you don't have to. Here is everything you need to know about the CrowdStrike 2026 Global Threat Report and what it means for your organization's security posture this year.
1. The Weaponization of AI: A Dual Threat
The most defining theme of the 2026 report is the exponential rise of AI in cyber warfare. Adversaries are demonstrating increasing fluency with AI tools, incorporating them into social engineering, intrusion tradecraft and information operations.
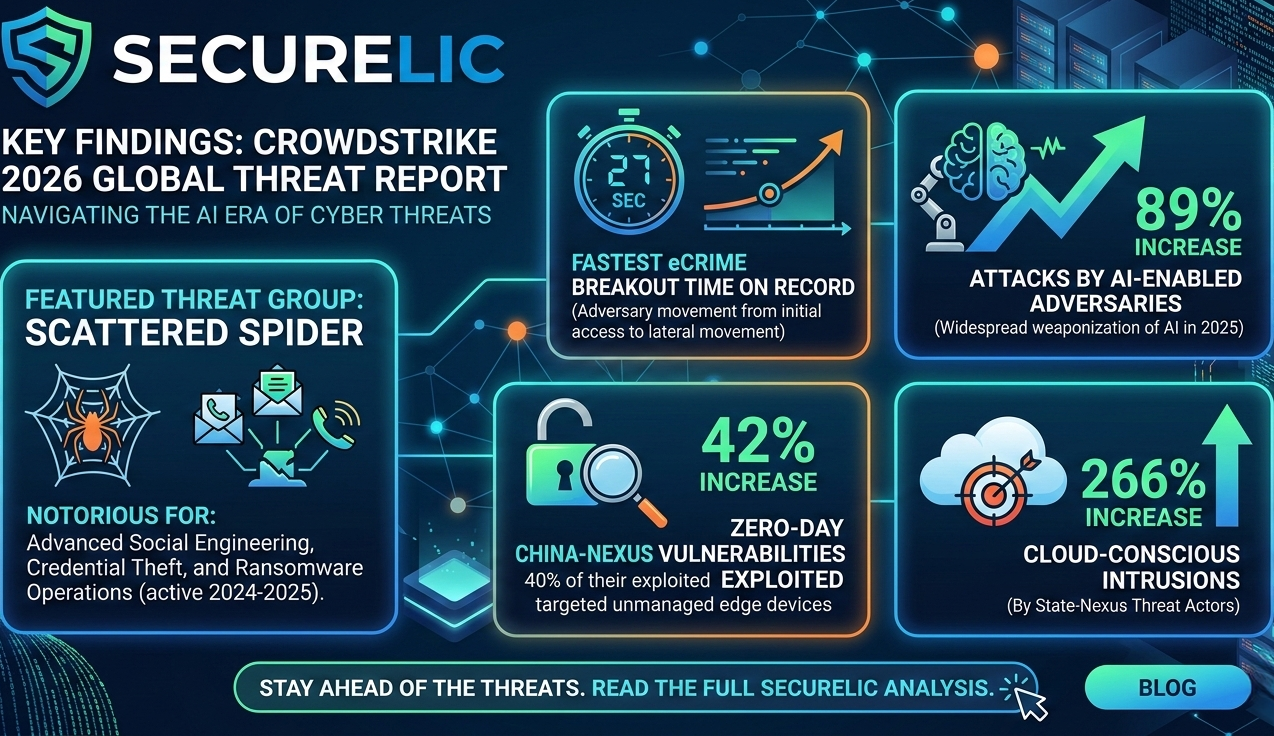
- 89% Increase: There was a massive 89% jump in attacks executed by AI enabled adversaries.
- The ChatGPT Effect: ChatGPT was mentioned in cybercriminal underground forums 550% more than any other AI model.
- Exploiting Legitimate Tools: Over 90 organizations had their legitimate, internal AI tools exploited by attackers to generate malicious commands and siphon sensitive data.
AI is acting as a massive force multiplier for threat actors, lowering the barrier to entry for less sophisticated hackers while giving elite state sponsored groups the ability to scale their operations effortlessly.
2. The Race Against Time: Breakout Speeds Hit Record Lows
"Breakout time" the time it takes for an adversary to move laterally from an initially compromised host to another within your network is the ultimate metric in cybersecurity. In 2026, the window for detection and response has virtually slammed shut.
- 27 Seconds: The fastest eCrime breakout time on record was clocked at an astonishing 27 seconds.
- 29 Minutes: The average eCrime breakout time plummeted to just 29 minutes, representing a 65% increase in speed compared to 2024.
Adversaries are no longer spending hours "breaking in." Instead, they are logging in using compromised credentials and moving laterally before security teams even receive an alert. In fact, a staggering 82% of detections in 2025 were entirely malware free, proving that legacy antivirus solutions are no longer sufficient.
3. Exploiting the Blind Spots: Edge Devices and the Cloud
With enterprise endpoints more heavily monitored than ever, adversaries have shifted their focus to the seams of the network: unmanaged edge devices, cloud environments and the supply chain.
- Zero-Day Surge: There was a 42% increase in zero day vulnerabilities exploited prior to public disclosure. Adversaries are weaponizing these unknown flaws faster than vendors can patch them.
- Edge Device Targeting: 40% of vulnerabilities exploited by China nexus threat actors specifically targeted edge devices (like routers, firewalls and VPNs), allowing them to establish a foothold outside the purview of traditional endpoint detection.
- Cloud Conscious Intrusions: State nexus threat actors orchestrated a massive 266% increase in cloud conscious intrusions, moving fluidly between identity providers, cloud infrastructure and virtual environments.
Past vs. Future: What to Expect in 2026
If we look back at previous years, the narrative was dominated by ransomware operators relying on spray and pray phishing and malicious attachments. Moving into 2026, the game has fundamentally changed.
We are now in the Year of the Evasive Adversary. Threat actors are utilizing cross domain tradecraft. They compromise identities, hijack AI agents and manipulate cloud misconfigurations. The historic $1.46 billion USD cryptocurrency heist recorded last year is a grim reminder of the financial devastation these modern tactics can achieve.
To survive 2026, organizations must shift from reactive, siloed security tools to proactive, unified visibility platforms that operate at the speed of AI.
How Securelic Can Keep You Ahead of the Curve
The CrowdStrike 2026 Global Threat Report makes one thing abundantly clear: defending against AI accelerated threats requires an AI native defense.
At Securelic, we specialize in closing the exact visibility gaps that today's adversaries exploit. We help organizations:
- Halt Cross Domain Attacks: Unifying visibility across your endpoints, cloud environments and identity providers to catch lateral movement.
- Secure the Edge: Identifying and locking down unmanaged edge devices before state sponsored actors can exploit them.
- Automate Response: Utilizing cutting edge AI and managed detection capabilities to stop breaches in seconds, not hours.
Don't let a 27 second breakout time catch your security team off guard. Contact Securelic to assess your 2026 security posture and ensure your defenses are ready for the AI era.
Reference: Data and statistics cited in this article are sourced directly