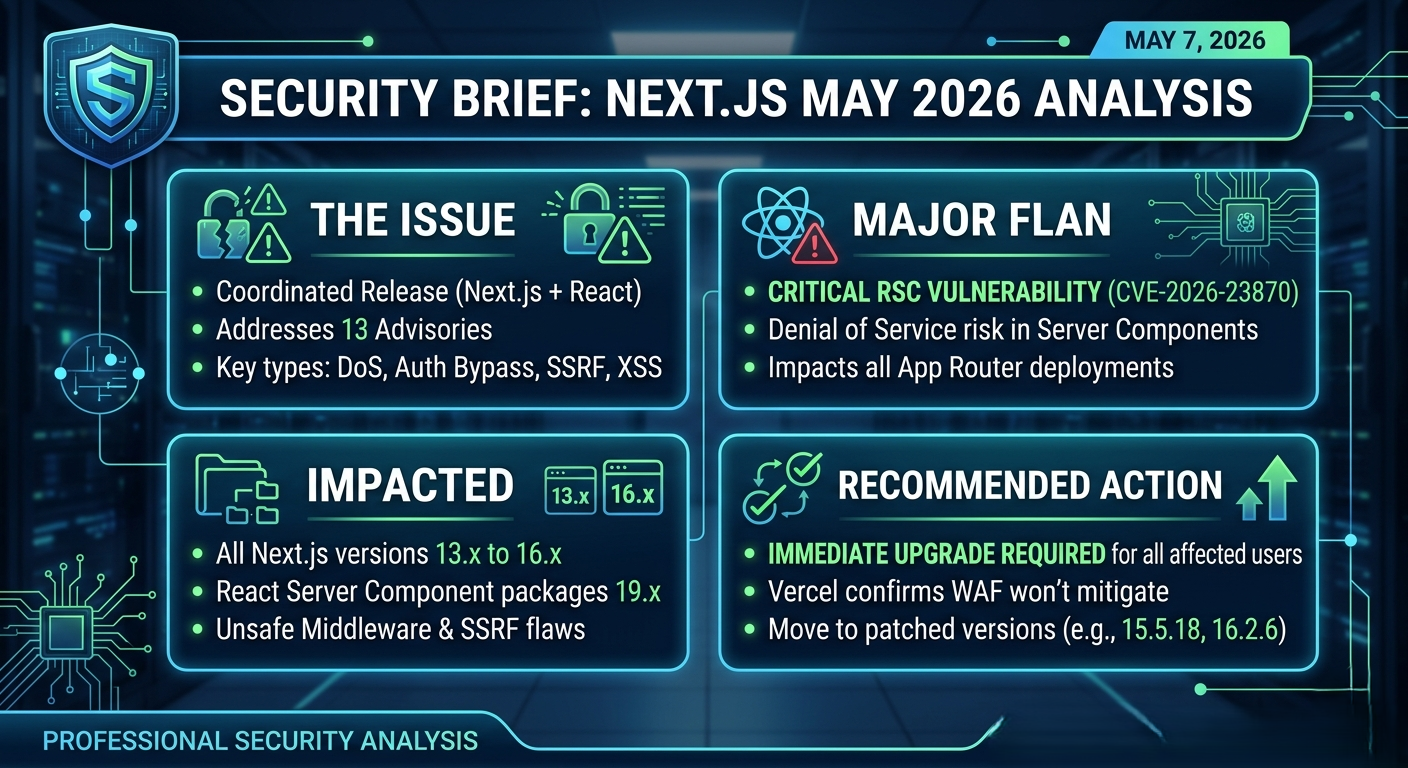
On May 7, 2026, Jimmy Lai (Head of Next.js) announced a massive coordinated security release addressing 13 distinct advisories. These vulnerabilities range from high-severity Denial of Service (DoS) to auth-bypassing middleware flaws. Most notably, this release includes a fix for a critical upstream React Server Components (RSC) vulnerability tracked as CVE-2026-23870.
At Securelic, we recommend that all organizations using Next.js versions 13.x through 16.x prioritize these updates immediately, as Vercel has confirmed these exploits cannot be reliably mitigated via WAF rules.
On May 7, 2026, Jimmy Lai (Head of Next.js) announced a massive coordinated security release addressing 13 distinct advisories. These vulnerabilities range from high-severity Denial of Service (DoS) to auth-bypassing middleware flaws. Most notably, this release includes a fix for a critical upstream React Server Components (RSC) vulnerability tracked as CVE-2026-23870.
At Securelic, we recommend that all organizations using Next.js versions 13.x through 16.x prioritize these updates immediately, as Vercel has confirmed these exploits cannot be reliably mitigated via WAF rules.
Other Critical Categories:
- Middleware & Proxy Bypass: Multiple "High" severity flaws were found where attackers could bypass authorization by injecting dynamic route parameters or using specific App Router segment-prefetch URLs.
- Server-Side Request Forgery (SSRF): Affects applications handling WebSocket upgrade requests, potentially allowing attackers to make internal network requests.
- Cross-Site Scripting (XSS): Found in applications using CSP nonces or
beforeInteractivescripts consuming untrusted input.
Impacted Versions & Mitigation Path
The following table summarizes the version requirements to secure your environment. If you are on an older version of Next.js 13 or 14, you must jump to the latest patched version in the 15.x or 16.x branch.
| Package | Affected Versions | Upgrade To (Patched) |
| Next.js 16.x | <= 16.2.5 | 16.2.6 |
| Next.js 15.x | <= 15.5.17 | 15.5.18 |
| Next.js 13.x / 14.x | All Versions | 15.5.18 or 16.2.6 |
| react-server-dom-* | 19.0.x / 19.1.x / 19.2.x | 19.0.6 / 19.1.7 / 19.2.6 |
Note: If you are using react-server-dom-webpack, react-server-dom-turbopack, or react-server-dom-parcel, ensure your lockfile reflects the React 19.x patches listed above.
Why You Can't Rely on Your WAF
A key takeaway from the Vercel advisory is the lack of WAF (Web Application Firewall) mitigations. Because many of these vulnerabilities especially the path bypasses and RSC exploits rely on how the framework internally parses URLs and prefetch headers, external filters struggle to distinguish malicious traffic from legitimate Next.js functionality.
Securelic Checklist for Developers:
- Audit your
package.json: Check for any Next.js version below 15.5.18. - Verify Peer Dependencies: Ensure your React packages (
react,react-dom, andreact-server-dom-*) are updated to the latest 19.x patch. - Test Middleware: If your app uses
middleware.jsfor RBAC (Role-Based Access Control), perform a regression test on your protected routes after patching.
Expert Advice from Securelic:
Security debt in modern frameworks like Next.js can accumulate fast. While 13 advisories at once might feel like a lot to digest, the move toward "Partial Prerendering" and "Server Functions" in 2026 means your attack surface is shiftng more toward the server. Patching is no longer "optional maintenance" it's your first line of defense.
Are you running a complex setup with custom middleware or a proxy layer that might be particularly sensitive to these bypass vulnerabilities?