The foundation of any modern cybersecurity strategy lies in creating an accurate and comprehensive map of your digital assets. When it comes to External Attack Surface Management (EASM), even a single overlooked subdomain can open the door to critical security vulnerabilities. This is where Subfinder, one of the most trusted utilities for cybersecurity professionals and penetration testing teams, comes into play.
If you are looking for a highly targeted, fast, and scalable subdomain finder, Subfinder is often the first tool that comes to mind. Let’s explore the capabilities of this powerful passive subdomain enumeration tool and its critical role in security audits.
What is Subfinder?
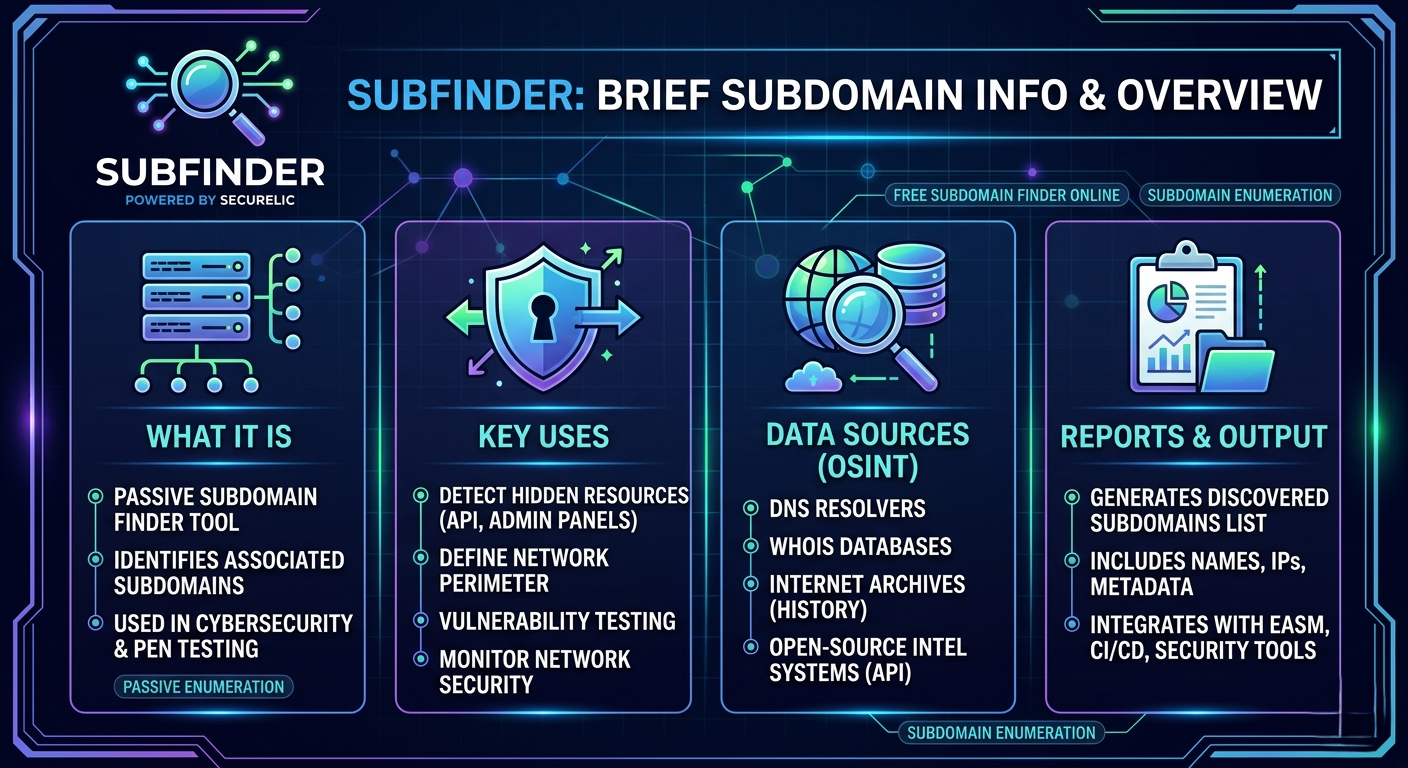
Subfinder is a high-performance utility written in Go, specifically designed for identifying subdomains associated with a specified domain. It is commonly employed in cybersecurity tasks, particularly for penetration testing, security audits, and threat intelligence. Thanks to its blazing-fast, modular, and continuously updated architecture, it has become one of the industry's go-to subdomain enumeration tools.
While many beginners might initially search for a free subdomain finder online, security engineers quickly realize that leveraging a robust, automation-friendly CLI tool like Subfinder provides unmatched scalability and control for integrating into continuous security workflows.
How Does Subfinder Work?
Unlike active scanning tools that send aggressive and noisy requests directly to target systems, Subfinder operates by primarily utilizing passive information-gathering techniques. It works by sending requests to DNS servers and analyzing the responses, allowing it to detect both known and unknown subdomains without directly tipping off the target.
To discover these subdomains, Subfinder pulls data from a diverse array of sources, including:
DNS Resolvers: Validates and analyzes records through rapid, parallel DNS queries.
WHOIS Databases: Scans registration data and associated networks within domain records.
Internet Archives: Extracts forgotten but historically active subdomains from platforms like the Wayback Machine.
Open-Source Intelligence (OSINT) Systems: Passively aggregates data from dozens of sources such as Shodan, Censys, VirusTotal, and GitHub.
Why is it Critical for Pen Testing and Security Monitoring?
Threat actors often bypass the heavily fortified main web applications, opting instead to target forgotten, unpatched, or development-stage subdomains (e.g., dev, staging, api-test). The visibility provided by Subfinder is crucial for several key reasons:
- Detecting Hidden Resources or Services: Helps uncover unconfigured API endpoints or forgotten administrative panels that are publicly accessible but not actively linked.
- Defining Network Boundaries and Perimeter: Maps out the clear digital footprint of an organization, defining exactly where security controls need to be applied.
- Vulnerability Testing and Detection: A thorough reconnaissance phase ensures that downstream vulnerability scanners (like OWASP ZAP or Nuclei) have a complete list of targets, leaving no blind spots.
- Network Security Monitoring and Control: Through automated, continuous workflows, it allows security teams to instantly detect new and potentially unauthorized subdomains added to the infrastructure.
Powerful Reporting and Architecture Integration
What elevates Subfinder from a simple discovery script to an enterprise-grade tool is its output management. As a result of its work, Subfinder can generate a structured report with information about the discovered subdomains, including their names, IP addresses, and other metadata.
The ability to output clean, standardized data in formats like JSON makes it incredibly easy to integrate into API-driven architectures. It fits seamlessly into continuous CI/CD pipelines, cloud-based SaaS security products, and centralized EASM platforms.
Conclusion
An effective cybersecurity posture starts with knowing exactly what you need to protect. Subfinder is a highly popular tool among information security specialists and penetration testers, as it allows for quick and effective subdomain discovery and information gathering. By integrating such powerful open-source utilities into modern, centralized security solutions, you can illuminate your blind spots and stay one step ahead in an ever-evolving threat landscape.